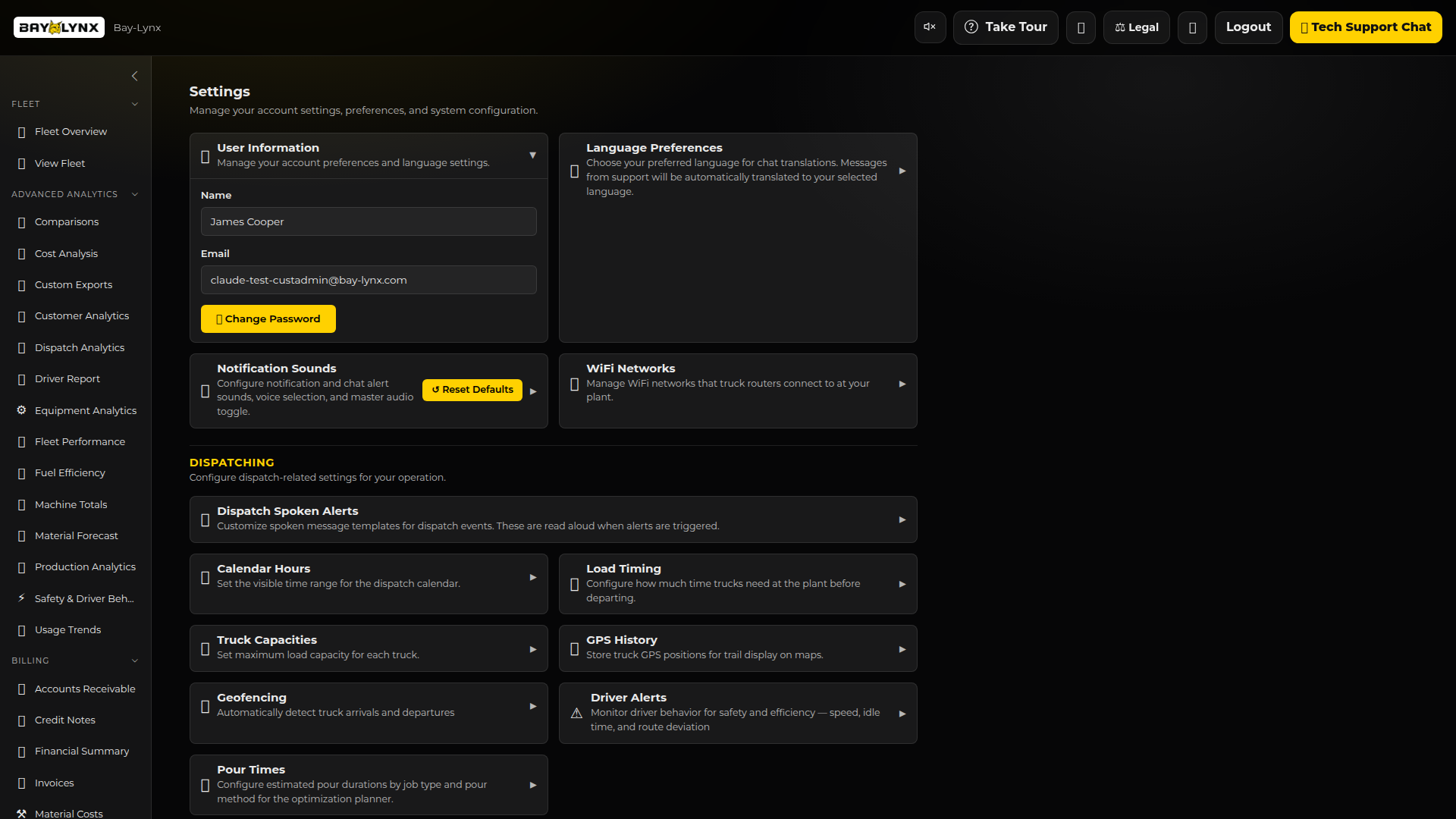
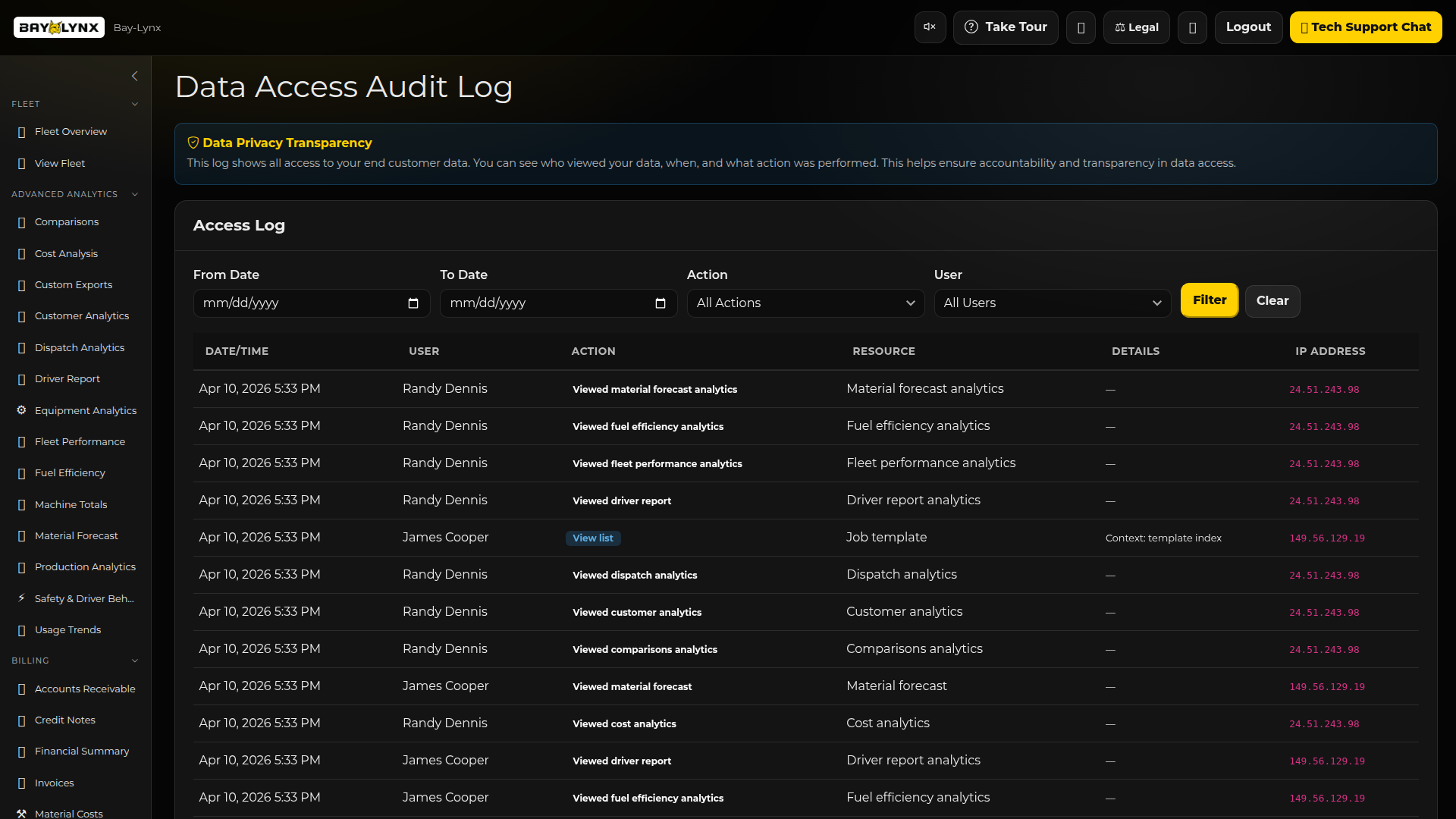
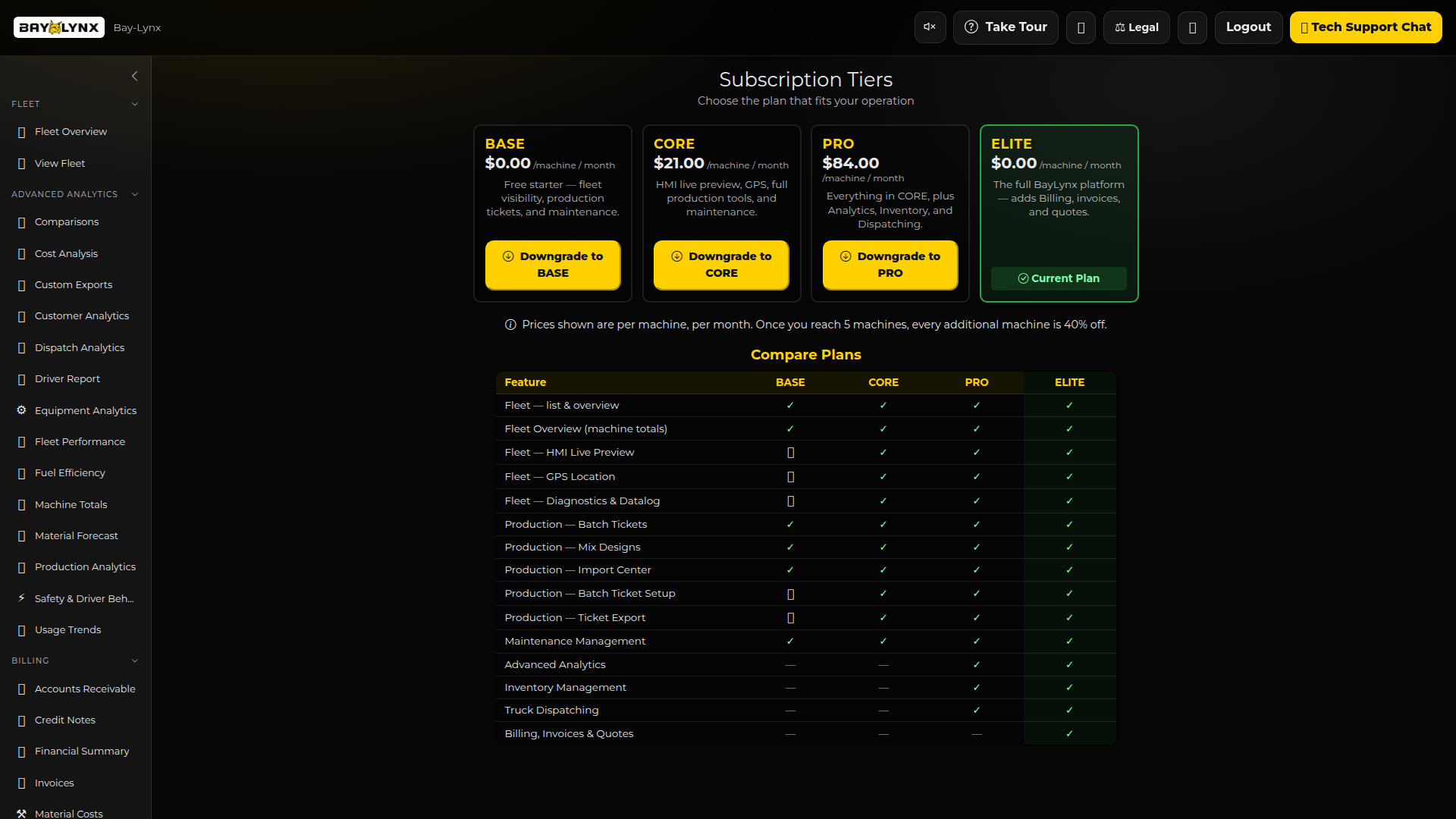
Multi-Tenant Security
Enterprise-grade security with role-based access control, two-factor authentication, complete audit logging, and strict data isolation between customer accounts.
Role-Based Access
Two-Factor Auth (2FA)
Audit Logging
Data Isolation
Session Management
IP Tracking